Cybersecurity researchers have flagged a new evolution of the GlassWorm campaign that delivers a multi-stage framework capable of comprehensive data theft and installing a remote access trojan (RAT), which deploys an information-stealing Google Chrome extension masquerading as an offline version of Google Docs.
“It logs keystrokes, dumps cookies and session tokens, captures screenshots, and takes commands from a C2 server hidden in a Solana blockchain memo,” Aikido security researcher Ilyas Makari said in a report published last week.
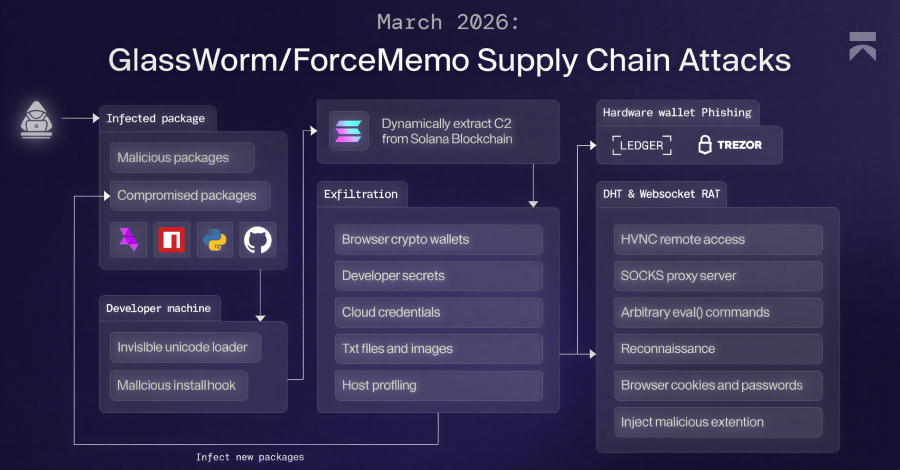
GlassWorm is the moniker assigned to a persistent campaign that obtains an initial foothold through rogue packages published across npm, PyPI, GitHub, and the Open VSX marketplace. In addition, the operators are known to compromise the accounts of project maintainers to push poisoned updates.
The attacks are careful enough to avoid infecting systems with a Russian locale and use Solana transactions as a dead drop resolver to fetch the command-and-control (C2) server (“45.32.150[.]251”) and download operating system-specific payloads.
The stage two payload is a data-theft framework with credential harvesting, cryptocurrency wallet exfiltration, and system profiling capabilities. The collected data is compressed into a ZIP archive and exfiltrated to an external server (“217.69.3[.]152/wall”). It also incorporates functionality to retrieve and launch the final payload.
Once the data is transmitted, the attack chain involves fetching two additional components: a .NET binary that is designed to carry out hardware wallet phishing and a Websocket-based JavaScript RAT to siphon web browser data and run arbitrary code. The RAT payload is fetched from “45.32.150[.]251” by using a public Google Calendar event URL as a dead drop resolver.
The .NET binary leverages the Windows Management Instrumentation (WMI) infrastructure to detect USB device connections and displays a phishing window when a Ledger or Trezor hardware wallet is plugged in.
“The Ledger UI displays a fake configuration error and presents 24 numbered recovery phrase input fields,” Makari noted. “The Trezor UI displays a fake “Firmware validation failed, initiating emergency reboot” message with the same 24-word input layout. Both windows include a ‘RESTORE WALLET’ button.”
The malware not only kills any real Ledger Live processes running on the Windows host, but also re-displays the phishing window if the victim closes it. The end goal of the attack is to capture the wallet recovery phrase and transmit it to the IP address “45.150.34[.]158.”
The RAT, on the other hand, uses a Distributed Hash Table (DHT) to retrieve the C2 details. In the event the mechanism returns no value, the malware switches to the Solana-based dead drop. The RAT then establishes communication with the server to run various commands on the compromised system –
- start_hvnc / stop_hvnc, to deploy a Hidden Virtual Network Computing (HVNC) module for remote desktop access.
- start_socks / stop_socks, to launch a WebRTC module and run it as a SOCKS proxy.
- reget_log, to steal data from web browsers, such as Google Chrome, Microsoft Edge, Brave, Opera, Opera GX, Vivaldi, and Mozilla Firefox. The component is equipped to bypass Chrome’s app-bound encryption (ABE) protections.
- get_system_info, to send system information.
- command, to execute attacker-supplied JavaScript via eval().
The RAT also force-installs a Google Chrome extension named Google Docs Offline on Windows and macOS systems, which then connects to a C2 server and receives commands issued by the operator, allowing to gather cookies, localStorage, the full Document Object Model (DOM) tree of the active tab, bookmarks, screenshots, keystrokes, clipboard content, up to 5,000 browser history entries, and the installed extensions list.
“The extension also performs targeted session surveillance. It pulls monitored site rules from /api/get-url-for-watch and ships with Bybit (.bybit.com) pre-configured as a target, watching for the secure-token and deviceid cookies,” Aikido said. “On detection, it fires an auth-detected webhook to /api/webhook/auth-detected containing the cookie material and page metadata. The C2 can also supply redirect rules that force active tabs to attacker-controlled URLs.”
The discovery coincides with yet another shift in GlassWorm tactics, with the attackers publishing npm packages impersonating the WaterCrawl Model Context Protocol (MCP) server (“@iflow-mcp/watercrawl-watercrawl-mcp) to distribute malicious payloads.
“This is GlassWorm’s first confirmed move into the MCP ecosystem,” Koi security researcher Lotan Sery said. “And given how fast AI-assisted development is growing – and how much trust MCP servers are given by design – this won’t be the last.”
Developers are advised to exercise caution when it comes to installing Open VSX extensions, npm packages, and MCP servers. It’s also recommended to verify publisher names, package histories, and avoid blindly trusting download counts. Polish cybersecurity company AFINE has published an open-source Python tool called glassworm-hunter to scan developer systems for payloads associated with the campaign.
“Glassworm-hunter makes zero network requests during scanning,” researchers Paweł Woyke and Sławomir Zakrzewski said. “No telemetry. No phone-home. No automatic update checks. It reads local files only. Glassworm-hunter update is the only command that touches the network. It fetches the latest IoC database from our GitHub and saves it locally.”