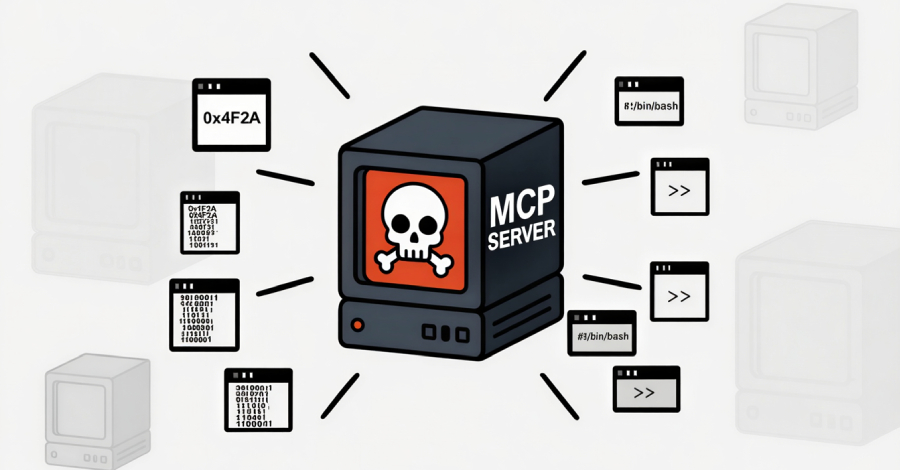
Keenadu Firmware Backdoor Infects Android Tablets via Signed OTA Updates
A new Android backdoor that’s embedded deep into the device firmware can silently harvest data and remotely control its behavior, according to new findings from Kaspersky. The Russian cybersecurity vendor said it discovered the backdoor, dubbed Keenadu, in the firmware of devices associated with various brands, including Alldocube, with the compromise occurring during the firmware […]
Continue Reading